Currently, this course is offered as an instructor-led 2-day online class. It is comprised of lectures, demonstrations, and 12 hands-on labs to help you master the different tools and techniques for proficiency in WiFi penetration testing and vulnerability assessment.
We will start with the IEEE 802.11 basics, about the standard and what each amendment brings to the table, as well as the channels and frequency bands, starting with the original 802.11 on the 2.4GHz ISM band, to the 802.11ax, that uses MIMO and operates on the 2.4, 5, and 6GHz bands, and also about 802.11be, aka WiFi 7, which will be finalized this year.
While these bands are license-free, we still have to abide by the ever changing regulations around the world, even during a penetration test, and you will learn how to ensure your system does.
You will also learn about the various network structures for WiFi networks, as well as the terminology, enabling you to understand the various tools we will be using.
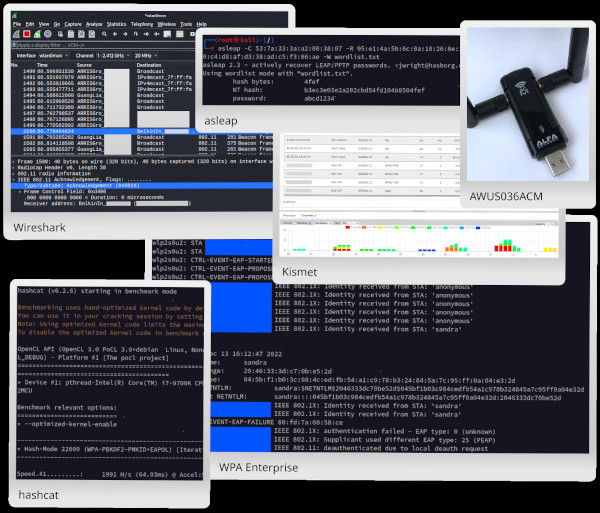
Hardware matters significantly when doing a WiFi penetration test or a vulnerability assessment, as not every WiFi adapter work, is dependable, or has the capabilities required for this type of work. We will discuss recommended adapters and their capabilities, as well as how to select the right one for the job.
Equally important is the software used, including the OS and the drivers. Hardware is useless without quality software. We'll briefly go over the available Linux distributions for WiFi penetration testing, wireless drivers, and other considerations when choosing hardware and software.
From here, we'll move into learning about the different frames that are encountered on WiFi networks, including a brief exploration with Wireshark and a number of packet capture files, as well as live capture.
Afterward, we will cover the various choices of encryption (and in one case, the lack of) of Wi-Fi networks:
For WPA, we'll go over what differentiate WPA Personal (Pre-Shared Key or PSK) and WPA Enterprise. We'll learn the details about WPA 4-way handshake, which is used on both Personal and Enterprise networks, and practice different techniques to exploit WPA-PSK networks, including leveraging rogue access points.
Then, we'll cover WPA Enterprise and EAP, with the numerous methods and encapsulations available when authenticating. We'll focus on PEAP-MSCHAPv2, and go over the details of this 2-phases exchange itself. We'll see how it looks in a packet capture and cover attacking and exploiting this type of network set-up.
Anyone beginning a career in information security or network administration can benefit from this course. It is designed as a beginner to intermediate course and can also be useful to information security professionals looking to expand their skill set and/or learn WiFi penetration testing.
This class combines course materials with 12 hands-on labs for practice. The following topics are covered in the course:
A recent computer with:
For the live class, a webcam is also required. Headset is optional but recommended.
The hands-on labs require:
We recommend the following hardware for the successful completion of the hands-on labs:
For best experience in the labs, we recommend the latest version of VMware Workstation/Player (17.5) or Fusion (13.5), along with a USB 3.0 port.
While not mandatory, we also suggest students have a basic familiarity with networking, Linux, and the command line.
In addition to using the hands-on labs for practice, we strongly believe that taking notes is an integral part of the learning process. For that reason, we recommend all students attend class with a notebook and pen or pencil. If you do prefer to take notes digitally, we recommend tools like OneNote, Obsidian, or any other text application of your choice.
Dual monitors are preferable as they offer the opportunity to have the class on one monitor, and the labs or note-taking on the other monitor.
All prices are in U.S. dollars.
Ready to start your journey?